Use Cases Showcase
Explore our demo applications showcasing iExec's confidential computing toolkit in action. Each use case shows real-world applications of privacy-preserving technologies.
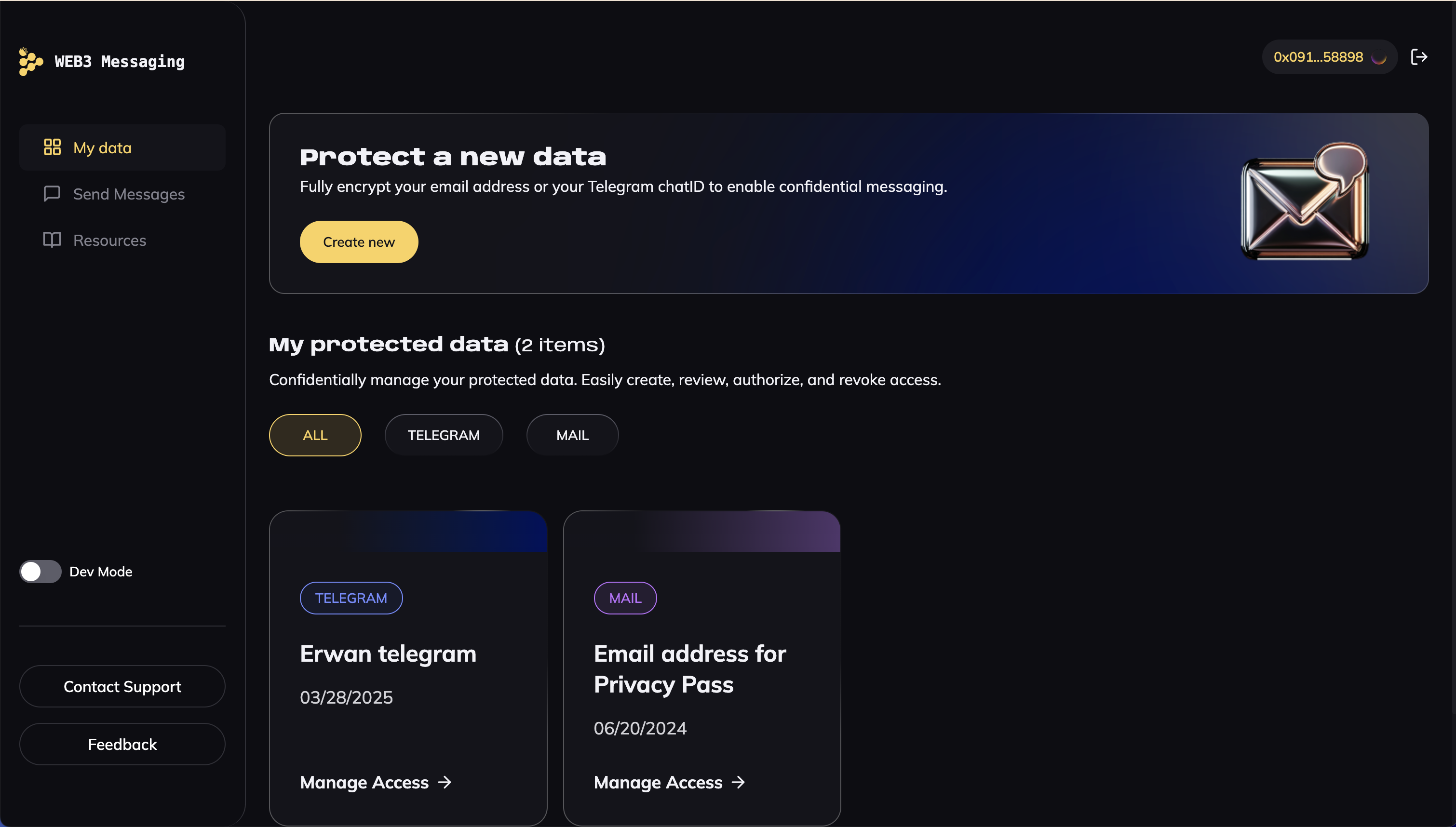
Web3 Messaging
Secure communication platform for Web3 users enabling privacy-preserving messaging through Web3Mail and Web3Telegram. Users maintain control over their data while enabling targeted communication and monetizing their engagement.
iExec Confidential AI
At the crossroads of DePIN and AI
iExec provides the confidential computing infrastructure for AI, enabling developers to protect and monetize the entire AI pipeline. With the Confidential AI framework, you can:
- Train models collaboratively.
- Monetize and reward contributors.
- Ensure integral, end-to-end encryption across the workflow.
End-to-end confidential AI pipeline
- Trusted Execution Environments (TEEs): Secure, tamper-proof enclaves for AI training and inference.
- Models and data stay encrypted at all times—processed without being exposed.
- Execution and results are traced on-chain, ensuring verifiability and accountability.

AI Agent
Execute ElizaOS AI agents with full confidentiality in iExec [TDX](/protocol/tee/intel-tdx) Trusted Execution Environments (TEEs)

MCP Server
A Model Context Protocol (MCP) compatible server to interact with the iExec protocol — built for Claude, agents, and AI tooling
Image Caption Matcher
The Image-Caption Matcher Project validates how well an image matches a textual description using Artificial Intelligence (AI)

Image Generator iApp
The Image Generator iApp is a Confidential Computing application that generates an image based on a provided text prompt. It leverages iExec's Trusted Execution Environments (TEE) and the CompVis/stable-diffusion-v1-4 model from Hugging Face for secure, private computation.